Incident Response Report: Malware Traffic Analysis
Operation BURNINCANDLE
Date: December 2, 2025
Tools: Wireshark, VirusTotal, ThreatFox
1. Executive Summary
Incident Overview
A network forensic analysis was conducted on captured traffic (PCAP) originating from the internal host BURNINCANDLE (10.0.9.14). The investigation confirmed a malware infection initiated via an unencrypted HTTP GET request. The host downloaded a GZIP-compressed payload from a malicious domain. Initial hash analysis of the exported file yielded no results; however, a pivot to domain-based threat intelligence confirmed the infrastructure as part of an IcedID (BokBot) banking trojan campaign.
2. Investigation Details & Infection Vector
| Initial Access | Victim connected to 188.166.154.118 over Port 80 via HTTP GET Request. |
| Payload Delivery | Encrypted GZIP payload (393 kB) downloaded. Validated via Wireshark. |
| Persistence | Observed immediate establishment of multiple HTTPS/TLS connections to external C2 IPs. |
Step 1: File Identification & Extraction
The analyst identified a suspicious file transfer within the HTTP traffic. Using Wireshark's "Export HTTP Objects" feature, the GZIP payload was extracted for analysis.
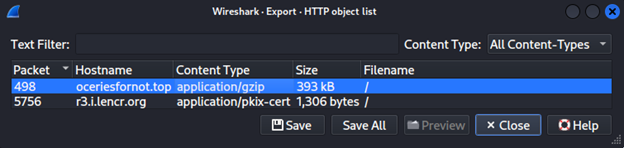
Figure 1a: Wireshark 'Export HTTP Objects' window showing the malicious GZIP payload.
(Click anywhere to close)
Step 2: Hash Verification
The extracted file (malware_payload.gz) was hashed using SHA256.
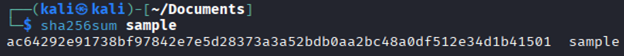
Figure 1b: Command line hash generation of the extracted payload.
(Click anywhere to close)
Step 3: Negative Lookup
A search of the file hash in VirusTotal returned 0 detections, indicating a unique or encrypted artifact.
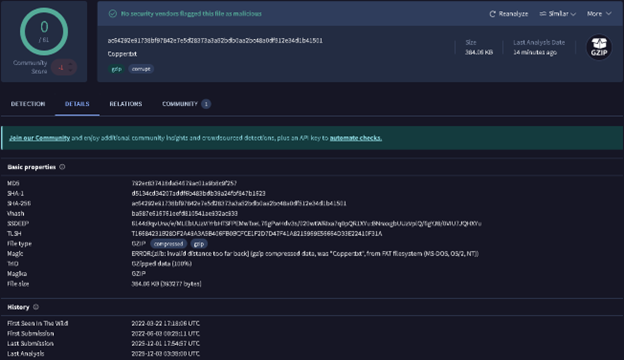
Figure 1c: VirusTotal search result showing 0 detections for the file hash.
(Click anywhere to close)
Step 4: Artifact Analysis
Further inspection of the payload revealed the file Copper.txt, a known artifact associated with IcedID encrypted configurations.
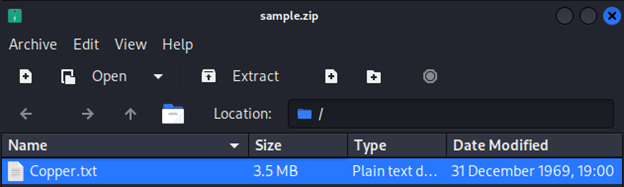
Figure 1d: Visual confirmation of the Copper.txt artifact within the payload.
(Click anywhere to close)
Step 5 & 6: Infrastructure Pivot
Shifted investigation focus from the file to the network infrastructure. Searching the source domain oceriesfornot.top confirmed it as a known Botnet C2 associated with the BokBot (IcedID) malware family.
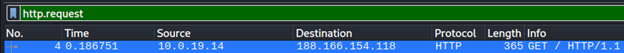
Figure 1e: Wireshark filter (http.request) isolating the initial malware download.
(Click anywhere to close)
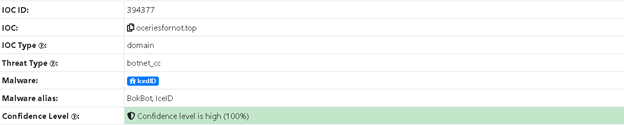
Figure 2: ThreatFox IOC database confirming the malicious domain is linked to BokBot/IcedID.
(Click anywhere to close)
3. Indicators of Compromise (IOCs)
Network Indicators
- Domain: oceriesfornot.top
- IP (C2): 188.166.154.118
- Protocol: HTTP (Port 80)
File Artifacts
- Filename: Copper.txt
- Type: Encrypted Config
- Family: IcedID / BokBot
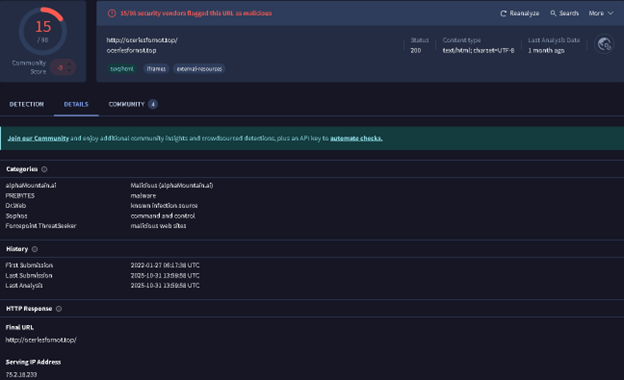
Figure 3: Threat intelligence validating the malicious C2 domain.
(Click anywhere to close)
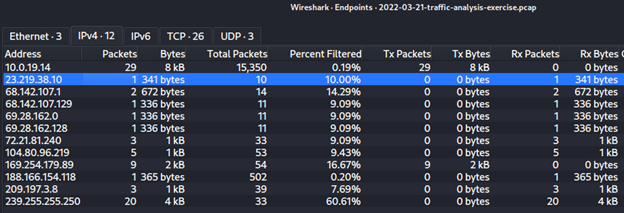
Figure 4: Wireshark Endpoints Statistics identifying external malicious IP connections.
(Click anywhere to close)
4. Remediation Recommendations
- Containment: Isolate the host 10.0.9.14 (BURNINCANDLE) from the network to prevent lateral movement or data exfiltration.
- Network Blockade: Configure firewall rules to deny all inbound/outbound traffic to
oceriesfornot.topand188.166.154.118. - System Restoration: Wipe and re-image the compromised system from a known clean backup.
- Credential Reset: Force a password reset for the user account associated with the compromised host.